- Originally Published on May 15, 2025
I’m Being Blackmailed: How to Deal with Online Blackmail
Online blackmail, also known as cyber extortion or sextortion, is a crime that occurs when someone threatens to reveal sensitive or embarrassing information about you unless you meet their demands. Blackmailers often seek money, but they may also demand additional intimate content or other favors. This form of extortion can take place through various online channels, such as email, social media, or dating apps. If this is happening to you, you’re not alone—and help is available.
If you are being blackmailed online, follow these steps:
- Stop all contact. Do not reply to the blackmailer or send them any money, personal content, or information.
- Tell someone you trust. A friend, parent, or advisor can help you stay calm and think clearly.
- Save all messages and evidence. Take screenshots and document everything before reporting the crime.
- Report the blackmail. Contact the platform where it occurred and report it to law enforcement or a cybercrime agency.
- Get legal help. You can speak with an experienced online blackmail attorney who understands how to stop the threats and protect your reputation.
The most important thing to know is this: it’s not your fault. Online blackmailers prey on fear and shame, but you do not have to go through this alone.
Many blackmailers give up when they realize you’re not going to pay or cooperate. And if anything is posted online, it may be possible to get it removed quickly with the help of legal professionals or reporting platforms.
At Minc Law, our team of attorneys has handled hundreds of online blackmail and digital extortion cases. We can take over communication with the blackmailer, remove damaging content from the internet, and coordinate with law enforcement to hold the perpetrator accountable.
In this comprehensive guide, we’ll walk you through how to identify online blackmail, respond safely, and get the trusted online blackmail help you need.
How to Spot The Warning Signs of Online Blackmail
Online blackmail doesn’t always start with a threat—it often begins with what seems like a harmless conversation. Many blackmailers use fake identities, flattery, and emotional manipulation to build trust before making any demands. Knowing how to spot early red flags can help you avoid falling into a digital extortion trap.
Here are some of the most common signs that someone may be trying to blackmail you online:
- Their story or identity feels inconsistent.
They may use a stolen photo, vague or generic bios, or avoid answering specific questions about themselves. If their profile seems too perfect or doesn’t line up with what they say in conversation, that’s a red flag. - They escalate the relationship unusually fast.
Online blackmailers often rush emotional intimacy, expressing affection quickly, complimenting you excessively, or suggesting private chats almost immediately after meeting. - They steer the conversation toward explicit content.
They might ask personal questions, initiate sexting, or push you to send intimate images or videos. Some may request that your face be visible, making the content more likely to leak later. - They avoid showing their real self.
They may claim their webcam is broken, refuse to video chat, or send seductive photos that appear staged or too professional. Often, these are stolen images used to build false trust. - They mimic your social network.
Some scammers try to look legitimate by following or friending people in your community—classmates, coworkers, or mutual contacts. This tactic is meant to make them seem more trustworthy and harder to question. - They use guilt, pressure, or threats early on.
Even before full-on blackmail begins, they may pressure you to act quickly (“Do you trust me?” “I thought we had something special”) or guilt you into complying. Any sign of emotional manipulation deserves caution.
How Online Blackmailers Target Their Victims
Online blackmailers use a wide range of tactics to manipulate and threaten victims. Their goal is always the same: to gain leverage over you and pressure you into doing something, whether that’s sending money, more images, or staying silent.
Below are some of the most common blackmail scenarios we’ve seen in online extortion cases:
1. Fake Profiles & Catfishing
The blackmailer pretends to be someone else—often an attractive person—using stolen photos and a fake identity. They might message you out of the blue with a flirty or explicit photo, then quickly steer the conversation toward sexual topics. Once you send an intimate image or join a private video chat, the tone shifts. Suddenly, they’re threatening to share the content with your friends, family, or employer unless you send money or more material.
This tactic is common on platforms like Instagram, Snapchat, Facebook, WhatsApp, and dating apps like Tinder or Bumble.
2. “I Hacked Your Device” Scams
In this scheme, the blackmailer claims they’ve gained access to your phone, computer, or email account and found compromising material, whether or not it actually exists. To make it sound more believable, they may include a password you once used (leaked from a past data breach) or mention details from your online presence.
In reality, they likely don’t have any real access—they’re bluffing and hoping fear will lead you to pay. These messages often come via email and may include cryptocurrency payment demands.
3. Deepfakes, AI Manipulation & Fake Content
With today’s technology, scammers can create fake but convincing images or videos using AI. They might take a regular photo of you from social media and generate a nude version (a “nudified” image), or use deepfake software to place your face on explicit content.
The blackmailer then uses this fake material to intimidate you, claiming they’ll release it unless you comply. Even if the content is fabricated, the fear it causes can be just as real.
4. Grooming & Long-Term Manipulation
Grooming is when someone builds a relationship with you over time, often pretending to care about you or developing romantic feelings. Once trust is established, they gradually push boundaries, asking for personal photos or intimate content. When you comply, they flip the dynamic, using the content as blackmail to force you into ongoing interactions, send more material, or keep quiet.
Grooming is especially dangerous when it targets minors. Any adult using these tactics to exploit a child is committing child sexual abuse, even if it happens entirely online.
5. Coercive Control in Personal Relationships
Not all online blackmailers are strangers. In some cases, a current or former partner threatens to share intimate content to manipulate you. They may not demand money, but instead use threats to control your behavior, such as keeping you from ending the relationship, isolating you from friends, or forcing you to follow their rules.
This kind of emotional abuse is known as coercive control, and it’s a form of domestic abuse that often includes digital threats.
Immediate Steps to Take to Deal With Online Blackmail
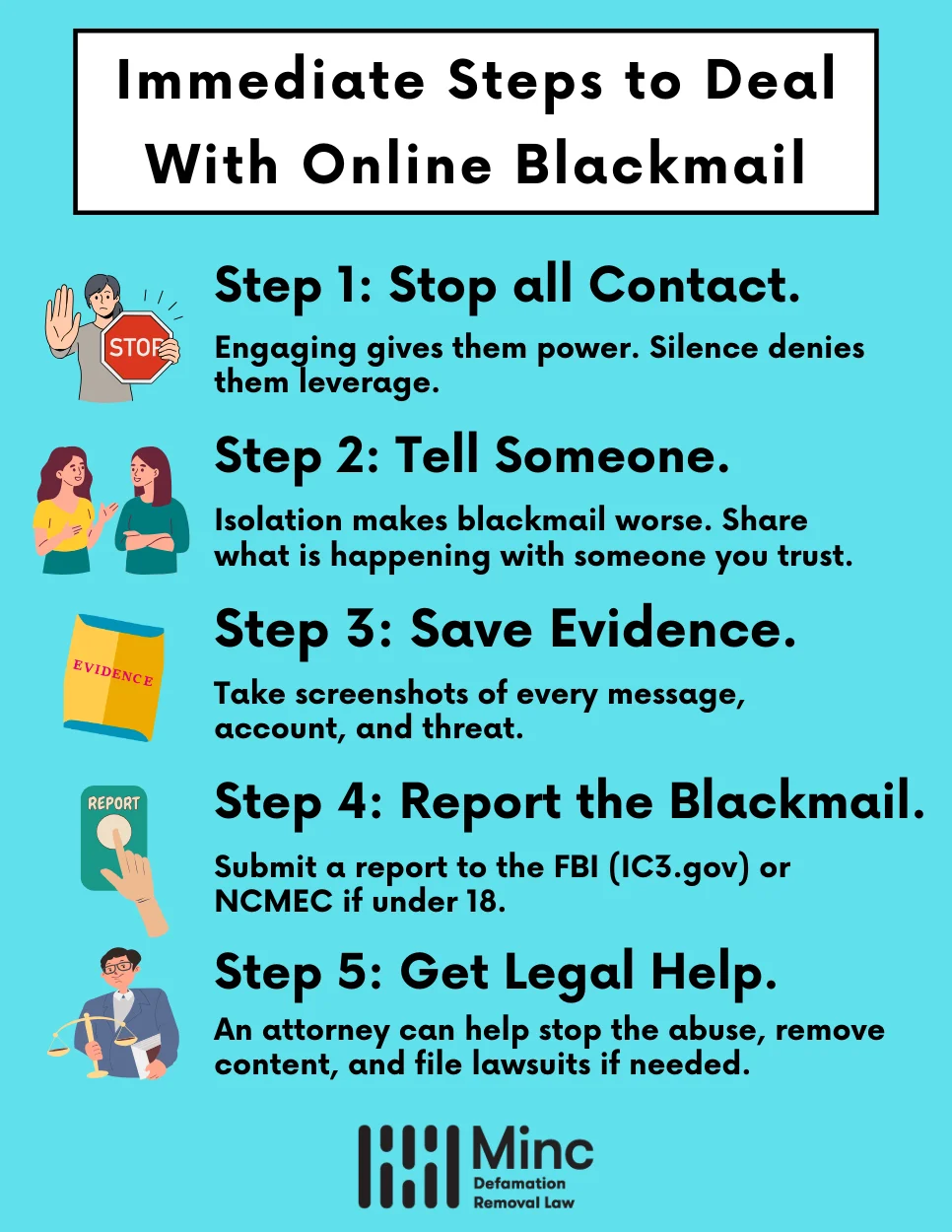
1. Stop All Contact With the Blackmailer
Not responding or ignoring online blackmail may carry risks, but so does engaging further with the perpetrator. Replying to their messages may give them even more information to use as leverage against you.
Engaging in further conversation can cause you more stress, while showing the scammer that you are a prime target. If the perpetrator knows they have your attention, they may escalate the situation with even more threats and demands.
Similarly, it may feel like your only option is to follow the scammer’s orders. But in most situations, paying an extortionist or giving in to their demands will not make the problem disappear.
2. Tell Someone You Trust
It’s easy to feel isolated when you’re being blackmailed, but support makes a huge difference. Whether it’s a friend, partner, parent, or mental health professional, sharing what’s happening can provide clarity and emotional grounding.
Crisis Support Hotlines
- Crisis Text Line: Text HOME to 741741 (24/7 support)
- National Suicide Prevention Lifeline: 988 (24/7 support)
- Cyber Civil Rights Initiative Crisis Helpline: 844-878-2274
- SAMHSA’s National Helpline: 1-800-662-HELP (4357)
Talking to someone who understands can reduce panic and help you make informed decisions. Remember, you don’t have to face this situation alone, and reaching out for support is a sign of strength, not weakness.
3. Save All Messages and Evidence
Even if it’s uncomfortable, preserving evidence is one of the most important things you can do. This information can help attorneys, platforms, or law enforcement act on your behalf.
Your first instinct may be to delete the messages and material the blackmailer sent you. But deleting evidence of online blackmail only makes it more difficult to hold them accountable. Reporting the harassment to law enforcement—and bringing a successful legal claim—requires proof.
Take screenshots of proof such as:
- All messages between you and the perpetrator,
- The sextortionist’s online profile(s),
- URLs of any harmful posts they made about you, and
- URLs of the sextortionist’s account(s).
Try to document the timeline of the online blackmail scam, from the first contact to their most recent threats.
4. Report the Blackmail
Online blackmail is a serious offense and should be reported as soon as you’ve collected evidence.
Report the Online Blackmail to Law Enforcement and Cybercrime Agencies
If you’re under 18, the best way to report is to contact the National Center for Missing & Exploited Children (NCMEC) at 1-800-THE-LOST (843-5678) or submit a report at CyberTipline.org.
If you’re 18 years or older, report to your local police department and the FBI’s Internet Crime Complaint Center at IC3.gov. You can also contact your local FBI Field Office directly.
Report the Online Blackmail to the Platform Where It Happened
You can also report the blackmailer to the social media or dating site where they targeted you. Every major social and dating platform has policies for reporting harassment and harmful online attacks.
By reporting them to the platform and having their profile suspended, you make it harder for the blackmailer to harass others. See the following resources for reporting online blackmail to various social media platforms:
| Social Media | Messaging Apps | Dating & Livestream | Gaming |
|---|---|---|---|
| Tinder | Roblox | ||
| Telegram | Bumble | Minecraft | |
| Snapchat | Discord | OnlyFans | Xbox Live |
| TikTok | Messenger | Twitch | |
| Twitter (X) | Skype | Hinge | |
| YouTube | Match | ||
If you need help gathering evidence and filing reports, an online blackmail attorney can assist you.
5. Get Legal Help From an Attorney
An internet attorney exclusively focuses on cases involving cyber harassment, defamation, and privacy violations. They can help you understand your rights, develop a strategy to protect your reputation, and pursue legal action against the blackmailer.
An internet attorney can also assist with content removal, working to have the blackmailer’s posts and messages removed from websites and social media platforms. They can draft cease-and-desist letters demanding that the perpetrator stop their harmful behavior or face legal consequences. In some cases, an attorney may recommend filing a civil lawsuit to seek damages for the emotional distress and reputational harm caused by the blackmail.
Possible Legal Outcomes
The legal consequences for online blackmail vary depending on the specifics of the case and the laws in your jurisdiction. In many states, blackmail is a felony offense punishable by substantial fines and imprisonment. If the blackmailer is convicted, they may face several years behind bars and be ordered to pay restitution to their victims.
In addition to criminal charges, victims of online blackmail may have grounds for a civil lawsuit. This can allow you to seek monetary damages for the harm caused by the blackmailer’s actions, such as:
- Emotional distress
- Reputational damage
- Lost income or business opportunities
- Therapy or counseling expenses
A successful civil case can provide a sense of justice and help you recoup some of the losses incurred due to the blackmail. However, it’s important to discuss the potential costs and benefits of pursuing legal action with your attorney, as the process can be time-consuming and emotionally taxing.
Regardless of the legal outcome, it’s crucial to prioritize your well-being throughout the process. Seeking support from loved ones and mental health professionals can help you cope with the trauma of online blackmail and begin to rebuild your sense of security and control.
Summary: Dealing With Blackmail Do’s and Don’ts
| What People Often Think or Do | What You Should Actually Know or Do Instead |
|---|---|
| Paying the blackmailer will make them stop. | It rarely ends there—most blackmailers escalate after payment. Don’t send money. |
| Deleting the messages will protect me. | Preserve all evidence (screenshots, messages, usernames)—it’s helpful for reporting. |
| Only people who share nudes get blackmailed. | Anyone can be targeted, even with fake or stolen content. It’s not your fault. |
| I should handle this on my own and not tell anyone. | Tell someone you trust and consider getting legal help—support is critical. |
| The police can’t do anything about online threats. | Online blackmail is a crime. Law enforcement and attorneys can help you. |
| I should confront or negotiate with the blackmailer. | Do not engage. Block the person, save the evidence, and report them instead. |
Frequently Asked Questions About Online Blackmail
Is Online Blackmail a Crime?
Yes, online blackmail, including sextortion, is considered criminal and is against the law in most countries.
In the United States, blackmail is typically prosecuted under federal law (18 U.S.C. § 873) and various state laws that address extortion and coercion. Penalties can include significant fines and imprisonment, which is why law enforcement takes reports of online blackmail seriously.
Do Blackmailers Follow Through on Their Threats?
One of the most common questions victims of extortion ask is whether blackmailers actually follow through with their threats. It may be empowering to know that many extortionists never follow through with their threats because they lose leverage once they do.
Perpetrators also know that following through with their threats may alert law enforcement to their activities, ending their illegal money-making scheme.
However, some blackmailers do follow through, so threats should always be taken seriously. This means you will want to seek professional advice and contact appropriate authorities if you are being blackmailed with nude photos or other content, but do not give in to their demands.
I’ve Already Paid the Blackmailer – Can I Cancel the Transaction or Get My Money Back?
If you’ve already paid a blackmailer, don’t panic—there may still be steps you can take to recover your funds and protect yourself from further demands.
If you transferred money from a bank account, contact your bank immediately to report the fraud and request assistance. Many banks have fraud departments that can help if you act quickly.
If you used a money transfer service, you may be able to cancel the transaction if you act fast enough. Contact the service’s customer support immediately.
Payment Service Recovery Options
- Cash App: Contact Support or call 1-800-969-1940
- MoneyGram: Call 1-800-926-9400 (US) for their fraud team
- PayPal: Resolution Center or call 1-888-221-1161
- Venmo: Contact Support or call 1-855-812-4430
- Western Union: Call 1-800-325-6000 to report fraud
- Zelle: Contact your bank that offers Zelle or call 1-844-428-8542
- Cryptocurrency: If you paid in cryptocurrency, contact a lawyer immediately as recovery is more complex
We Can Help You Navigate Online Blackmail
At Minc Law, we understand the fear and uncertainty that comes with being blackmailed online. Our experienced attorneys have deep experience in helping victims regain control of their digital lives and put an end to blackmail threats.
We can:
- Provide clear, objective advice tailored to your specific situation
- Communicate with the blackmailer on your behalf
- Secure your online accounts and digital presence
- Remove sensitive content if it has been posted online
- Work with law enforcement when appropriate
- Help you move forward with confidence and peace of mind
Our team has successfully helped hundreds of online blackmail victims, and we’re ready to fight for you, too. Don’t face this alone. Contact us today for a confidential consultation and take the first step toward resolving this situation and protecting your reputation.
Is online blackmail a crime?
Yes. Online blackmail, including sextortion, is a criminal offense in most countries. In the United States, it is typically prosecuted under federal law (18 U.S.C. § 873) as well as various state extortion and coercion statutes. Penalties can include significant fines and imprisonment.
What should I do first if I’m being blackmailed online?
Stop all contact with the blackmailer immediately. Do not reply to their messages, send money, or provide any personal content or information. Engaging further can give them more leverage and signal that you are a responsive target. Tell someone you trust, save all evidence, and seek professional help.
Should I pay the blackmailer to make them stop?
No. Paying a blackmailer or giving in to their demands rarely makes the problem go away. In most cases, it encourages the perpetrator to escalate with even more demands. Instead, preserve all evidence, report the crime to law enforcement, and consult with a qualified internet attorney.
Do blackmailers actually follow through on their threats?
Many blackmailers never follow through because they lose their leverage once content is released. They also risk alerting law enforcement to their activities. However, some perpetrators do carry out their threats, so every situation should be taken seriously. Seek professional advice and report the crime promptly.
What evidence should I save if I’m being blackmailed?
Document everything. Take screenshots of all messages between you and the blackmailer, their online profile(s), any URLs of harmful posts, and the URLs of their accounts. Record the full timeline from first contact to the most recent threats. This evidence is critical for law enforcement investigations and any legal proceedings.
Where do I report online blackmail?
If you are under 18, contact the National Center for Missing & Exploited Children (NCMEC) at 1-800-THE-LOST or report at CyberTipline.org. Adults should file a report with their local police department and the FBI’s Internet Crime Complaint Center at IC3.gov. You should also report the blackmailer directly to the social media or dating platform where the harassment occurred.
Can I be blackmailed with fake or AI-generated images?
Yes. With advancing technology, scammers can create convincing fake images or videos using AI deepfake tools. They may take a regular photo from your social media and generate manipulated explicit content, then threaten to release it. Even though the content is fabricated, the emotional impact and reputational risk can be very real. An attorney can help you respond and get fake content removed.
I already paid the blackmailer. Can I get my money back?
It depends on the payment method and how quickly you act. Contact your bank immediately if you transferred funds from an account. For services like Cash App, PayPal, Venmo, or Zelle, reach out to their fraud or support teams right away. Cryptocurrency payments are more complex to recover, so consult with an attorney immediately. Acting fast is essential.
What if the blackmailer already posted my content online?
If content has been posted, it may still be possible to get it removed quickly. An experienced internet attorney can work with platforms, search engines, and hosting providers to take down harmful material. Legal professionals can also issue takedown requests and pursue further action against the perpetrator.
What legal action can I take against an online blackmailer?
Online blackmail can be pursued through both criminal and civil channels. Criminal charges may result in fines and imprisonment for the perpetrator. Victims may also file a civil lawsuit to seek monetary damages for emotional distress, reputational harm, lost income, and therapy expenses. An internet attorney can help you understand your options and build a case.
How can an internet attorney help with online blackmail?
An internet attorney can take over communication with the blackmailer on your behalf, work to remove damaging content from the internet, help secure your online accounts, coordinate with law enforcement, and pursue legal action. They understand the tactics blackmailers use and can develop a strategy tailored to your specific situation.
Is it my fault that I’m being blackmailed?
No. Online blackmailers are criminals who prey on fear and shame. Regardless of the circumstances, the fault lies entirely with the person committing the crime. You are not alone, and there are professionals who can help you navigate this situation safely and confidentially.
Get Your Free Case Review
Fill out the form below, and our team will review your information to discuss the best options for your situation.
This page has been peer-reviewed, fact-checked, and edited by qualified attorneys to ensure substantive accuracy and coverage.



